3D rendering of a computer chip jiang jie feng/Shutterstock
Hertzbleed, a newly identified attack that could be used to grab information from computer chips, has captured the attention of technology security researchers – and technology news websites. Here’s what you need to know about the story.
What is Hertzbleed?
It is a new computer hack that takes advantage of a power-saving feature common to modern computer chips in order to steal sensitive data. It has been demonstrated in the lab and could be used by hackers in the wild.
Most chips use a technique called dynamic frequency scaling, or CPU throttling, to increase or reduce the speed with which they carry out instructions. Ramping the power of the CPU up and down to match demand makes them more efficient.
In the past, hackers have shown that they can read these power signatures and learn things about the data being processed. This can give them a foothold to break into a machine.
The team behind Hertzbleed found that you can actually do something similar remotely by watching carefully to see how quickly a computer completes certain operations, then using that information to determine how it is currently throttling the CPU. Demonstrating that such attacks can be performed remotely makes the issue much more dangerous because remote attacks are much easier for hackers to carry out.
What does it mean for you?
Intel declined a request for interview by New Scientist, but said in a security alert that all of its chips are vulnerable to the attack. The company said that, through such an attack, it “may be possible to infer parts of the information through sophisticated analysis”.
AMD, which shares chip architecture with Intel, also issued a security alert listing several of its mobile, desktop and server chips as vulnerable to the attack. The company didn’t respond to a request for comment.
Chipmaker ARM was also approached by New Scientist, but didn’t answer questions about whether it was working to avoid similar problems with its own chips.
One major issue is that even if your personal hardware isn’t affected, you could still fall victim to Hertzbleed. Thousands of servers around the word will store and process your information, archive your data and run the services you use daily. Any of these may be running on hardware that is vulnerable to Hertzbleed.
Intel says that the attack can take “hours to days” to steal even a tiny amount of data, so Hertzbleed is more likely to leak small snippets of data rather than large files, email conversations and the like. But if that snippet of data is something like a cryptographic key, then its impact can be significant. “Hertzbleed is a real, and practical, threat to the security of cryptographic software,” say the researchers who discovered the flaw, on their website.
How was it discovered?
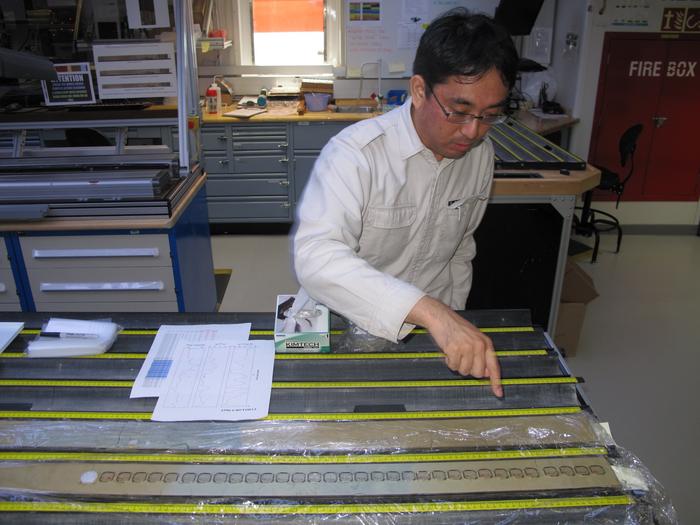
Hertzbleed was created by a group of researchers from the University of Texas at Austin, the University of Illinois Urbana-Champaign and the University of Washington in Seattle. They say that they disclosed their discovery to Intel in the third quarter of last year, but that the company asked for it to be kept quiet until May this year – which is a common request designed to allow a company to fix a flaw before it becomes common knowledge.
Intel allegedly then asked for an extension to 14 June, but has apparently released no fix for the problem. AMD was informed of the problem in the first quarter of this year.
Details of the vulnerability have now been published in a paper on the researchers’ website and will be presented at the USENIX Security Symposium later this summer.
“Side channel power attacks have been long known about, but this is a troubling evolution of the art,” says Alan Woodward at the University of Surrey, UK. “The story of its discovery and how it was kept under wraps is a cautionary tale for what else might be out there.”
Can it be fixed?
Neither Intel nor AMD are releasing patches to fix the problem, claim the researchers on their website. Neither company responded to questions posed by New Scientist.
When attacks that watched for changes in a chip’s speed, or frequency, were first discovered in the late 1990s, there was a common fix: write code that only used “time invariant” instructions – that is, instructions that take the same time to carry out regardless of what data is being processed. This stopped an observer gaining knowledge that helped them read data. But Hertzbleed can get around this strategy and can be done remotely.
Because this attack relies on the normal operation of a chip feature, not a bug, it could prove tricky to fix. The researchers say that a solution would be to turn off the CPU throttling feature on all chips, globally, but warn that doing so would “significantly impact performance” and that it may not be possible to fully stop frequency changes on some chips.
More on these topics: